Problem for SSL/TLS Traffic Boost
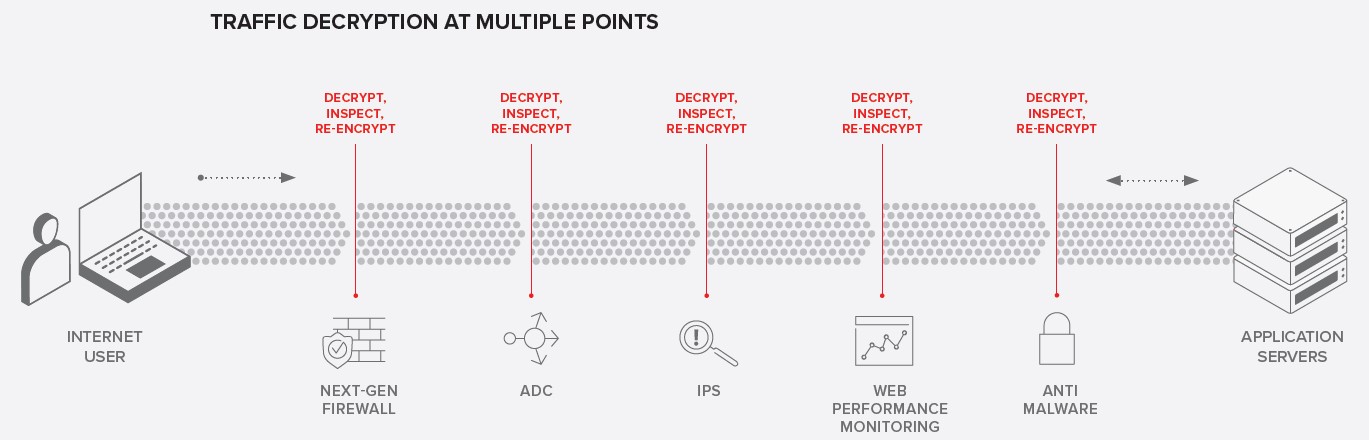
• The need to inspect traffic with greater scrutiny has grown exponentially as the threat landscape has evolved and encryption has become ubiquitous. Security teams deploy many technologies to detect threats to their applications(e.g. NGFW, WAF, and IPS). While these technologies require SSL/TLS decryption repeated at each point in the inspection chain in a traditional infrastructure.
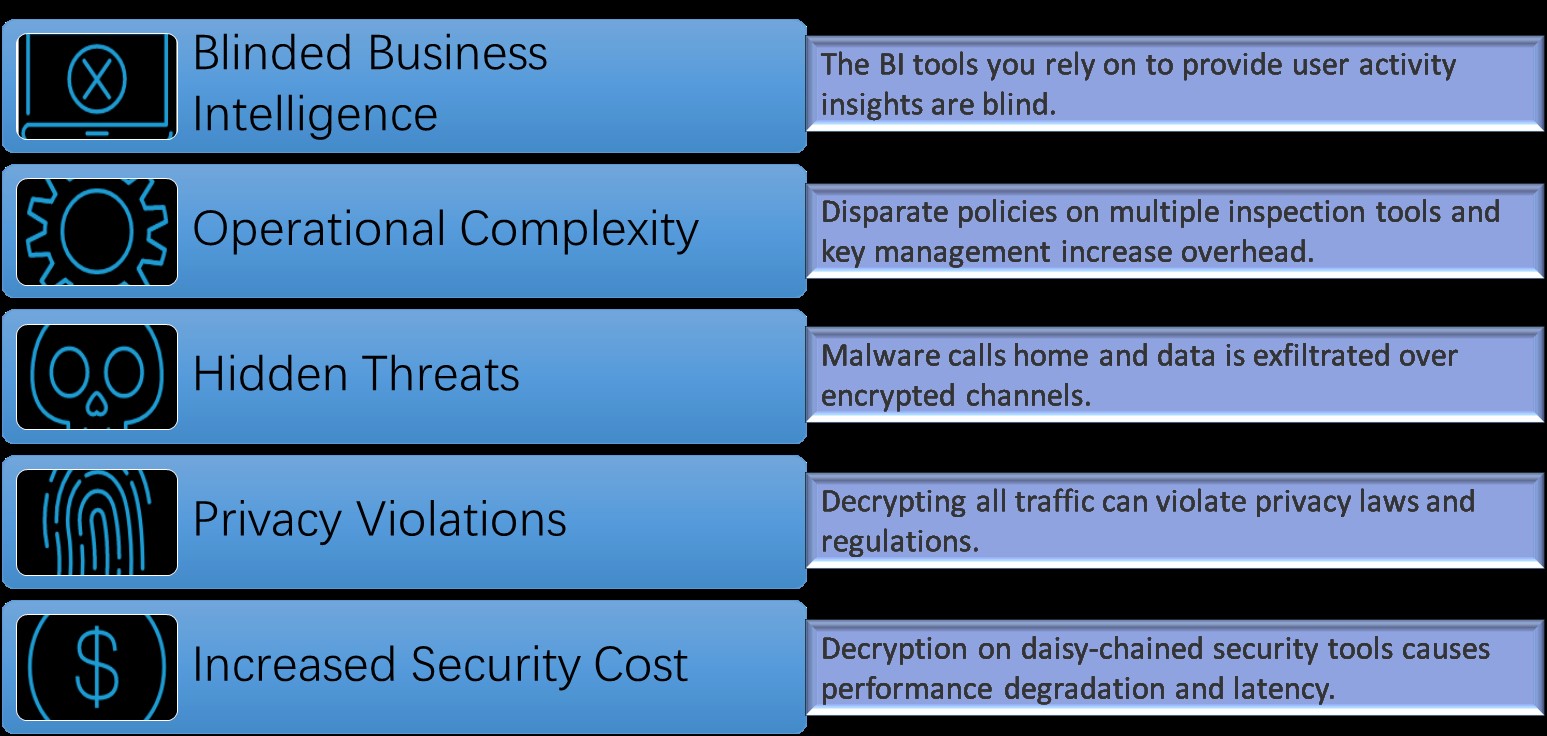
• Many organizations have responded by creating decryption zones in the DMZ for inspection by multiple devices, but it’s usually a static path where all decrypted traffic is inspected by the same chain of devices. While this strategy does boost performance and lower management overhead, it can introduce scaling problems. It may also limit the environment to less secure crypto by restricting the use of the cipher suites required for forward secrecy. Finally, the process can be inefficient because your security devices are inspecting everything instead of identifying and inspecting only the suspicious traffic.
• With the explosion of HTTPS traffic, decryption has become a requirement to enable application-layer traffic management decisions. Organizations frequently leverage an Application Delivery Controller (ADC) to provide visibility for other systems beyond the application server. A relatively new challenge is the requirement to provide visibility for multiple third-party inspection technologies on the same application connection.
Challenge Overview with SSL/TLS Encryption
KEYS TO ENCRYPTED THREAT PROTECTION: VISIBILITY INTO AND ORCHESTRATION OF ENCRYPTED TRAFFIC
• Enables visibility into SSL/TLS traffic with centralized decryption/encryption function for inspection across multiple security tools.
• Provides high-performance decryption of inbound and outbound SSL/TLS traffic, enabling security inspection to expose threats and stop attacks such as phishing, spear phishing, and ransomware.
• Dynamically chains security devices, independently monitors and scales them, and intelligently manages decryption across the entire security chain via a contextual classification engine, reducing administrative costs while utilizing security resources more efficiently.
• Shortens the typically cumbersome, time consuming change management process by orchestrating the security stack, simplifying equipment changes and mitigating their detrimental impact.
• Flexibly integrates into even the most complex architectures, centralizing SSL decrypt/encrypt functions and delivering the latest encryption technologies across the entire security infrastructure.
• Scales security services with high availability, leveraging F5’s best-in-class load balancing, health monitoring, and SSL offload capabilities.
F5 SSL Orchestrator
• Decrypting and re-encrypting traffic is computationally intensive, and many inspection tools—like next-generation firewalls and malware protection platforms—are simply unable to decrypt at scale. But visibility into encrypted traffic is not enough. The daisy chain of decryption and re-encryption through multiple security devices induces unnecessary latency and complexity. Policy-based orchestration breaks the daisy chain to most effectively stop malware and protect user privacy.
• F5 SSL Orchestrator was designed and purpose-built to enhance SSL/TLS infrastructure, provide security solutions with visibility into SSL/TLS encrypted traffic, and optimize and maximize your existing security investments. SSL Orchestrator delivers dynamic service chaining and policy-based traffic steering, applying context-based intelligence to encrypted traffic handling to allow you to intelligently manage the flow of encrypted traffic across your entire security stack, ensuring optimal availability. Designed to easily integrate with existing architectures and to centrally manage the SSL/TLS decrypt/encrypt function, F5 SSL Orchestrator delivers the latest SSL encryption technologies across your entire security infrastructure. With SSL Orchestrator’s high-performance encryption and decryption capabilities, your organization can quickly discover hidden threats and prevent attacks at multiple stages, leveraging your existing security solutions.
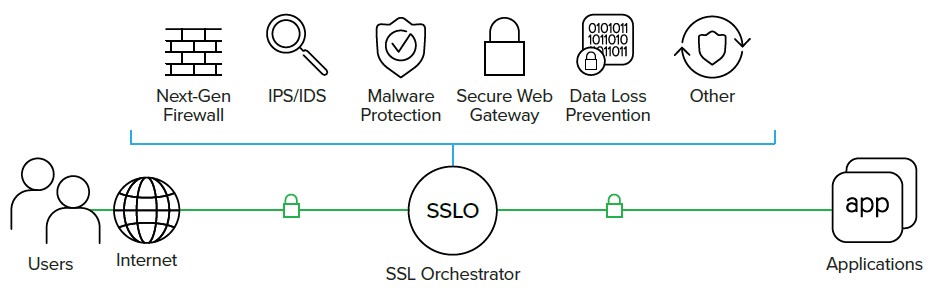
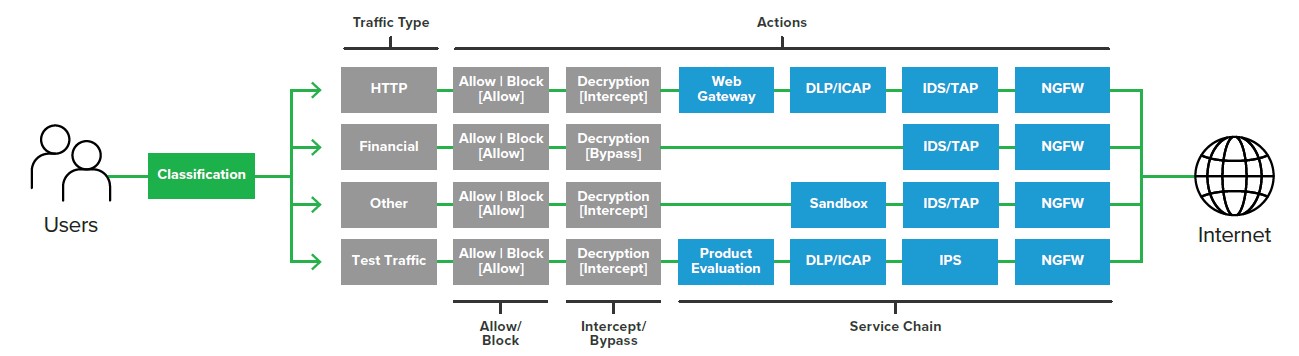
CONFIGURE DYNAMIC SERVICE CHAINING BASED ON CONTEXT
• SSL Orchestrator dynamically chains security services, including anti-virus/malware products, intrusion detection systems (IDS), IPSs, NGFWs, secure web gateways (HTTP proxy services), and DLPs. It leverages classification metrics such as domain name, content category, geolocation, IP reputation, and other policies that determine whether to decrypt traffic and which services traffic should be sent to. The policy-based traffic steering capabilities of SSL Orchestrator also increase administrative efficiency and reduce administrative cost by removing key and certificate management from your security infrastructure.