SSA - Intelligent Analysis of Network Data
Keeping up to date with security event logs and gaining insights into cyber incidents is a challenging task. SSA Network Data Analysis Engine is an agentless security event log analysis system developed by McFray Technology, which collects network device logs and samples through standard syslog protocol and netflow protocol to obtain network information.
SSA supports almost all major commercial firewall brands, including Juniper, NetScreen, Fortinet, Palo Alto, and many more. It helps network administrators understand network usage, hide security device brand differences, and access network security events and logs through a unified user interface.
Because the security appliance generates a large number of traffic logs, SSA's high-performance retrieval engine supports high-performance query, aggregation, and sorting of massive log data, so that administrators can accurately retrieve the information they need from the vast number of events.
Given the high-risk nature of potential security breaches, you need to stay informed of any suspicious activity that appears in your firewall event logs.

The SSA system is equipped with a robust alerting system that is able to send instant alerts when suspicious activity occurs, such as notifications based on objective indicators such as excessive bandwidth usage. You can also use pre-configured rules or create custom rules to help you better understand the relationships between various events and track anomalies.
SSA helps you set effective rules and policies by providing powerful event correlation, allowing you to take full advantage of your firewall deployment to increase system security. You can set rules for network and firewall events in real-time.
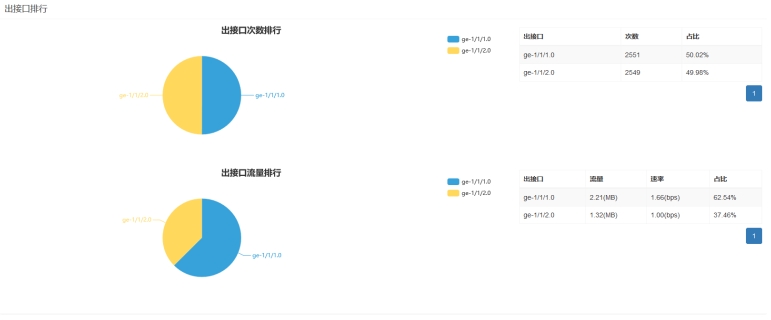
The SSA network data analytics engine supports data visualization, which allows users to optimize firewall policies by centrally managing and analyzing all firewall logs and gain more flexibility when verifying that devices are working as expected after policy changes or new policies are added.
In addition to having access to real-time logs, it's important to store historical logs to facilitate compliance forensic analysis, which may require a review of events from a few weeks ago. SSA can archive network event logs and provide historical event query and backtracking.
SSA is deployed as a virtual machine, eliminating the need for additional hardware, ensuring a low total cost of ownership.